Most of you are familiar about Cross Site Request Forgery (CSRF) vulnerability, it is one of the most common vulnerabilities; it was listed in OWASP Top 10 – 2013.
Previously, I had found and reported CSRF in an Intel website, by exploiting that vulnerability an attacker could remove items from an authenticated user’s shopping cart. such actions are common attack scenarios regarding CSRF.
In this case (phpMyAdmin), a database admin/Developer can be tricked into performing database operations like DROP TABLE using CSRF. It can cause devastating incidents! The vulnerability allows an attacker to send a crafted URL to the victim and if she (authenticated user) clicks it, the victim may perform a DROP TABLE query on her database.
What is phpMyAdmin?
phpMyAdmin is a free and open source administration tool for MySQL and MariaDB. As a portable web application written primarily in PHP, it has become one of the most popular MySQL administration tools, especially for web hosting providers using cPanel.
phpMyAdmin is widely used to manage the database for various websites created with WordPress, Joomla and many other CMS.
What is CSRF vulnerability?
CSRF stands for Cross Site Request Forgery.
According to OWASP, “A CSRF attack forces a logged-on victim’s browser to send a forged HTTP request, including the victim’s session cookie and any other automatically included authentication information, to a vulnerable web application. This allows the attacker to force the victim’s browser to generate requests the vulnerable application thinks are legitimate requests from the victim. ”
In simple terms, An attacker can create a crafted URL and lure the victims (with active session) to perform dangerous operations without their knowledge.
CSRF is a critical vulnerability and was listed in OWASP Top 10 -2013. A feature of phpMyAdmin was using a GET request and after that POST request for Database operations such as DROP TABLE table_name; GET requests must be protected against CSRF attacks. In this case, POST requests were used which were sent through URL (for bookmarking purpose may be); it was possible for an attacker to trick a database admin into clicking a button and perform a drop table database query of the attacker’s choice. However, it is difficult for a remote attacker to gather these information to craft a URL.
I also found that post requests could be converted into GET requests using burp’s ‘change request method’ feature. and it could be executed directly from a URL even after removing the token. by using this method, I was able to add a working wordpress admin user. an attacker would need cPanel session id and database name. other table names like wp_users can be guessed easily.
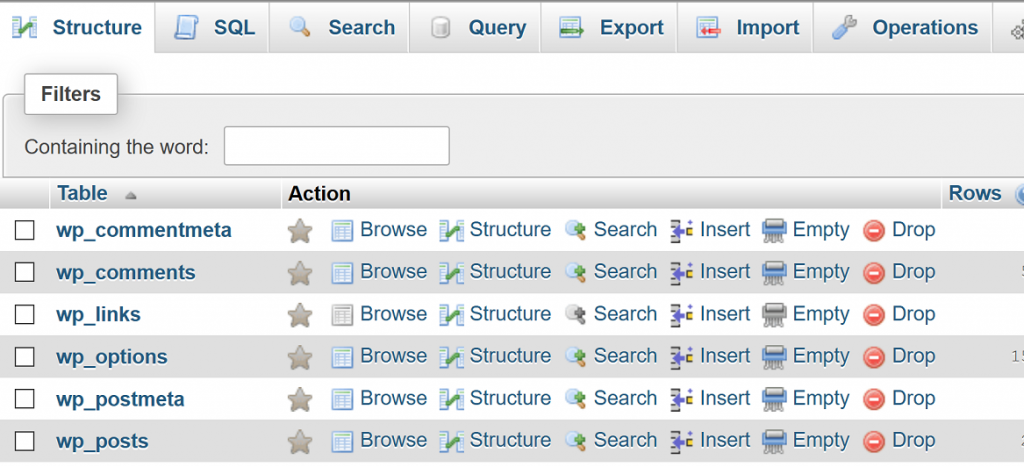
The URL for performing database operations was being saved in browser history. If a user executes a query on the database by clicking insert, DROP etc. buttons, the URL will contain database name and table name. This vulnerability can result into disclosure of sensitive information as the URL is stored at various places such as browser history, SIEM logs, Firewall Logs, ISP Logs etc.

This CSRF attack worked even when the user was authenticated in cPanel and phpMyAdmin was closed after use. In order to exploit this vulnerability, user interaction is required. so, severity for this vulnerability is Medium.
Here’s the proof of concept video for this vulnerability:
Know More About CSRF from OWASP:
https://www.owasp.org/index.php/Cross-Site_Request_Forgery_(CSRF)
The vulnerability is patched now. So, I request all the phpMyAdmin users to update it to v 4.7.7 or newer.
https://www.phpmyadmin.net/downloads/
It was nice to work with the team to resolve this issue, I am thankful to Madhura Jayrante, Security coordinator for phpMyAdmin for resolving this issue. I have been credited on phpMyAdmin security announcement page for reporting this security issue
Update: CVE-2017-1000499 has been assigned for this Security Flaw.
Security Announcement for this vulnerability can be found here:
https://www.phpmyadmin.net/security/PMASA-2017-9/
This issue was featured in The Hacker News!
https://thehackernews.com/2018/01/phpmyadmin-hack.html
Looking forward to find more bugs in open source products!



